Cybercriminals running phishing operations are now making use of SEO specialists that break Google’s rules to get themselves placed above legitimate search results to lure victims.
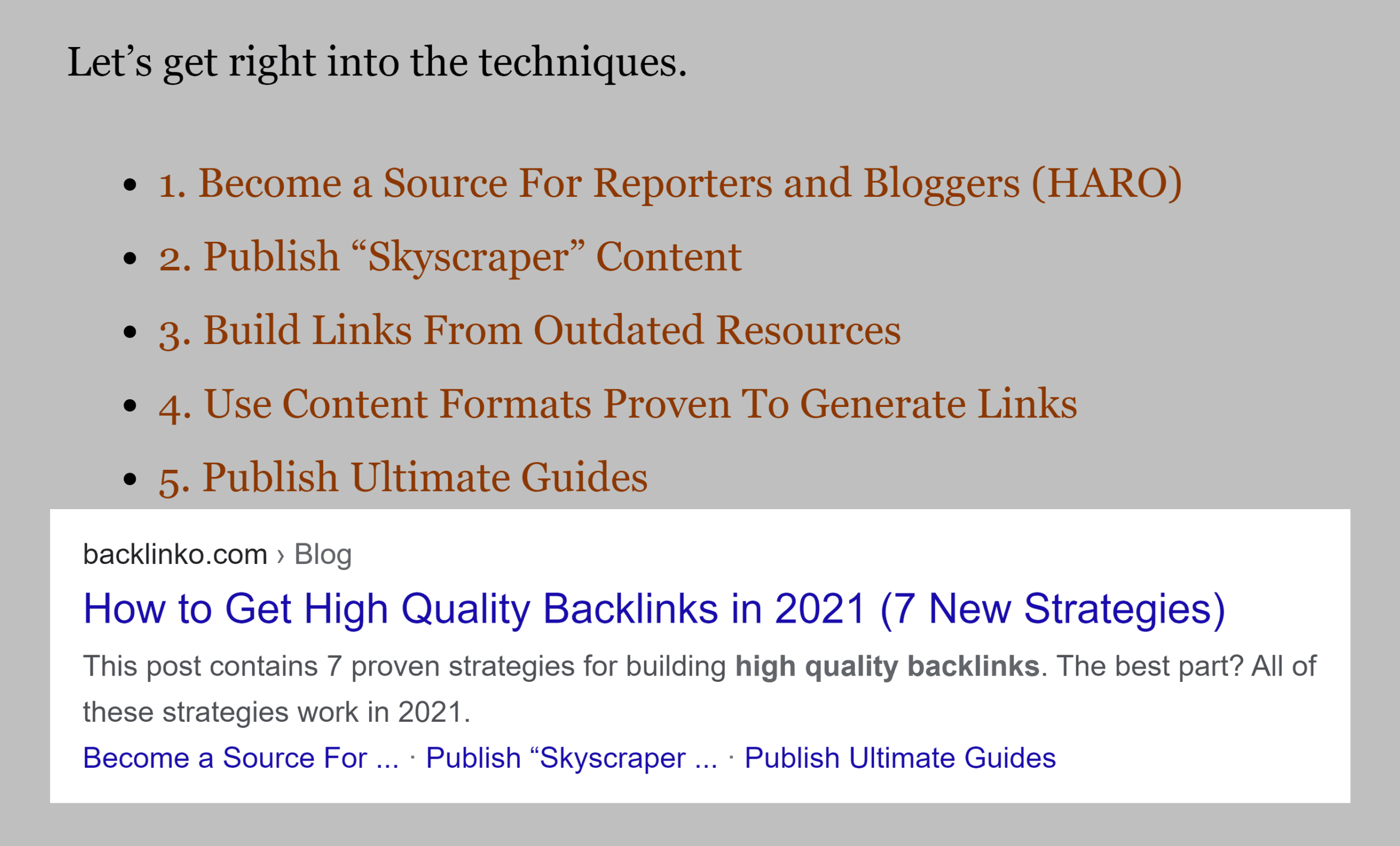
Phishing site operators now use special illegal search engine optimization tactics to show their pages above legitimate websites in search results. See the article : 11 SEO best practices for a mobile-first strategy.
Researchers at security firm Cybersixgill said these “black hat SEO” practices have become so popular that those who practice the skill can sell their services in the dark web hacking forums for $ 70-500 a month to phishing site operators.
Unlike traditional SEO techniques, which follow the guidelines set by search engines, black hat SEO practitioners violate the rules set by Google and Microsoft to play the system and promote phishing pages.
Adi Bleih, a dark web analyst at Cybersixgill, told SearchSecurity that some of the dirty tricks used by phishing attackers include filling in keywords, redirecting links to other sites, and using paid links.
“The difference is that black hat SEO is a tactic used to rank a website that violates search engine guidelines,” Bleih said. “Legit SEO focuses on creating the best results on the web, not just that it seems to be.”
As a result, phishing sites become much more effective at attracting users to their pages and collecting credentials and login information. While there is a risk that search engines will hit sites and remove them for violating SEO rules, the additional traffic for phishing site operators is worth it if it is properly balanced.
“In this case, the actions of the participant endanger the lifetime of the domain,” Bleih explained. “If he uses black hat SEO techniques more often, search engines can” punish “him and may be blocked or removed from the search engine data.”
Although the increase in the effectiveness of phishing attacks due to SEO is a threat in itself, the findings also pose a greater problem for administrators and defenders. Underground cybercrime markets have now developed to the point where specialized services can develop as a support ecosystem for groups conducting large-scale cybercrime and fraud operations.
SEO poisoning has been used by cybercriminals in the past, most recently in a campaign to spread SolarMarker from an information asset and backdoor. However, the Cybersixgill report showed that this practice is now widely available to a wide range of actors and groups at risk.
“This is what happens in the world of phishing and fraud, where you can find actors who create packages for phishing sites – background and front-end developments, admin panels, encrypted mail, etc. – and actors who specialize in marketing and SEO,” Bleih said.
“This should worry us – users who come to different sites based on search engine results.”
Dig Deeper on Data security and privacy
proxy hacking
SolarMarker malware spread through advanced SEO poisoning
Hack Friday: This Christmas, fight back against cyber criminals
Search engine poisoning: How are poisoned results detected?
Hacking can seriously harm your site. Read also : Action Comics # 1042 Preview: What About SEO?. This can affect your site’s presence in the SERPs and potentially cause you to perform multiple manual actions in the search console, as noted by Google.
What does botnet stand for?
A bot network is a network of hijacked computers and devices that are infected with bot malware and are remotely controlled by a hacker. On the same subject : GoDumpster Media Launches SEO Strategic Initiative for Container Rental Companies: Increasing Online Visibility and Web Visits. The botnet is used to send spam and launch distributed denial of service [DDoS] attacks and may be hired to other cybercriminals.
What is an example botnet? Smaller botnets can be among hundreds or thousands of infected machines, and larger ones can be exposed to millions of computers. Examples of well-known botnets that have emerged in recent years are Conficker, Zeus, Waledac, Mariposa and Kelihos.
Are botnets illegal?
Criminal behavior The use of the botnet is illegal and in many cases punishable as a criminal offense. Once exposed, the owners of these computers are at risk. Criminals have access to personal information stored on a computer and to communication with a computer.
Is it illegal to use a botnet?
Americans are suffering extensive and widespread invasions of privacy and financial losses from these hackers. Current criminal law prohibits the creation of a botnet because it prohibits hacking into computers without permission. It also prohibits the use of botnets to commit other crimes.
Can botnets be used for good?
Legitimate robot networks exist. Although the term “botnet” is generally associated with cybercrime and malware, it should come as no surprise that there are in fact perfectly legitimate and fully useful botnets, better known as “distributed computing systems”. work around the world.
Are botnets still a thing?
More than three years after its first appearance, the Mirai botnet remains one of the biggest threats to the Internet of Things. Learn about its variants and how to protect them. The Mirai botnet has been a constant security threat on the Internet of Things since its release in the fall of 2016.
Can you get caught using a botnet?
In some cases, criminal charges may be brought. In other cases, the management of the botnet is compromised and the robot network operator considers that their means of generating revenue are similarly compromised.
What is a botnet and how do they work?
A botnet refers to a network of hijacked devices connected to the Internet that are installed with malicious code called malware. All of these infected devices are known as robots and are remotely controlled by a hacker / cyber criminal known as a “bot herder.”
What a botnet can do?
A botnet is a set of devices with an Internet connection, each of which runs one or more robots. Botnets can be used to carry out DDoS (Distributed Denial-of-Service) attacks, steal data, send spam, and allow an attacker to access a device and its connection.
Is creating a botnet illegal?
Are botnets illegal? Installing malware on a victim’s computer without the victim’s consent to build a botnet is illegal and may be illegal.
What is a botnet virus?
Botnets are computer networks that are infected with malware (such as computer viruses, keyloggers, and other malicious software) and are remotely controlled by criminals, usually for financial gain or to launch attacks on websites or networks.
Is my computer infected with botnet?
Signs that your computer may be infected with bot malware include the following: Frequent computer crashes for no apparent reason. Slow internet connection. Problems shutting down your computer (shutting down takes time or doesn’t turn off completely / correctly)
How do you check if my PC is a botnet?
5 signs that your computer is part of a botnet
- # 1) Slow Internet. A slow internet is an indication that your computer is part of a botnet. …
- # 2) Unexpected shutdowns. If your computer shuts down or restarts unexpectedly, it may be part of a botnet. …
- # 3) Certain programs cannot be closed. …
- # 4) OS cannot be updated. …
- # 5) Malware detected.
What is botnet Attack example?
The attack involved using a Trojan horse program to infect devices. Since its creation, several variants have been presented. An example of this is CrytoLockerransomware. In 2009, Damballa infected 3.6 million hosts with the botnet.
Is SEO a hacker?
SEO hacking is a fast testing process designed to effectively increase the organic traffic of web assets. While traditional SEO strategies look at steady growth, SEO hacking finds unusual ways to gain traction quickly.
What is SEO in cybersecurity? Search engine optimization (SEO) is a comprehensive web strategy that incorporates SEO tactics and techniques that make your website more visible to search engines such as Google and Bing.
Is SEO real?
Don’t be fooled: SEO doesn’t die, but it develops much more than it did years ago. If you’ve been discussing whether or not to invest in SEO for your business, read on to find out why SEO isn’t going to die in 2021, it’s actually booming.
Is SEO really that important?
SEO is made up of several elements, and knowing what they are and how they work is the key to understanding why SEO is so important. In short, SEO is crucial because it makes your website more visible and means more traffic and opportunities to turn potential customers into customers.
Is SEO worth it in 2020?
While some traditional marketing methods may become obsolete, SEO will remain until 2020. Whether you invested in SEO early or are just getting started, it can still be a major driver of traffic and traffic to your website.
Is SEO even real?
Short answer: YES! SEO is more important than ever! It is still one of the most powerful digital marketing strategies that will deliver long-term results. You need to use the right techniques.
Is SEO a waste of money?
SEO is not dead. It is not a waste of money if and when it is done correctly. The grass on the other side is no greener; where it is watered, it is greener. If you take care of your website, it will take care of you!
What are SEO hacks?
On-page SEO hacks: Maximize organic traffic
- Increase your CTR by adding a year to your SEO headline. …
- Optimize your images with descriptive text. …
- Make your URLs SEO-friendly. …
- Get more traffic by adding keywords related to your content. …
- Write descriptive meta descriptions to increase your rankings.
How are DDoS attacks prevented?
You can rely on the following types of network security to protect your business from DDoS attempts: firewalls and intrusion detection systems that act as a barrier to controlling traffic between networks. Antivirus and anti-malware software that detects and removes viruses and malware.
What prevents DDoS attacks from being denied? Strengthening their security stance: This includes strengthening all devices with an Internet connection to prevent compromises, installing and maintaining anti-virus software, creating firewalls configured to protect against DoS attacks, and following strong security practices to monitor and manage unwanted traffic.
What is a DDoS attack is it preventable?
Although DDoS attacks cannot be prevented, steps can be taken to make it more difficult for an attacker to make a network unresponsive. Architecture. To protect resources against DDoS attacks, it is important to make the architecture as resilient as possible.
Can DDoS attacks be prevented using VPN?
Generally, VPNs can stop DDoS attacks. The main advantage of a VPN is that it hides IP addresses. With a hidden IP address, DDoS attacks cannot detect your network, making it much harder to target you.
What’s a DDoS attack?
DDoS Attack stands for “Distributed Denial-of-Service (DDoS) Attack” and is a cybercrime in which an attacker floods a server with Internet traffic to prevent users from accessing connected network services and sites.
What are some ways DDoS attacks can be prevented?
10 ways to prevent a DDoS attack
- Know your network traffic. …
- Create a denial response plan. …
- Make your network resilient. …
- Practice good cyber hygiene. …
- Increase your bandwidth. …
- Take advantage of anti-DDoS hardware and software. …
- Move to the cloud. …
- Know the symptoms of the attack.
Can a DDoS attack be prevented?
ISPs are undoubtedly experts in DDoS mitigation and have a unique position to protect their customers’ networks from malicious traffic. ISPs can detect and filter out potential DDoS packets before they reach your border, preventing all attacks from using all your available bandwidth.
What is DDoS attack and how can you protect against it?
DDoS attacks at a glance Protecting your website from DDoS attacks involves implementing a number of solutions to deal with spoofed traffic from hackers to overload your server resources. Website owners should not wait for their site to be attacked before taking action.
Which of the following can be used to protect against DDoS attacks?
To protect your web application from DDoS attacks, you can use the AWS Shield DDoS Protection Service, which AWS automatically provides to all AWS customers at no additional charge.
What are the DDoS attacks and explain how do you protect from DDoS attacks?
10 ways to prevent a DDoS attack
- Know your network traffic. …
- Create a denial response plan. …
- Make your network resilient. …
- Practice good cyber hygiene. …
- Increase your bandwidth. …
- Take advantage of anti-DDoS hardware and software. …
- Move to the cloud. …
- Know the symptoms of the attack.
What’s a DDoS attack?
DDoS Attack stands for “Distributed Denial-of-Service (DDoS) Attack” and is a cybercrime in which an attacker floods a server with Internet traffic to prevent users from accessing connected network services and sites.
Can DDoS attacks be prevented using VPN?
Generally, VPNs can stop DDoS attacks. The main advantage of a VPN is that it hides IP addresses. With a hidden IP address, DDoS attacks cannot detect your network, making it much harder to target you.
Can you be Ddosed with a VPN?
Do you get DDoS protection when using a VPN? Yes. The service hides your IP address so that hackers can no longer use it to target your network. Just make sure you choose a VPN that actually provides DDoS protection, such as StrongVPN.
Does Nordvpn protect from DDoS?
Protect yourself from DDoS attacks Our in-game VPN protects your computer from unintentional Denial of Service (DDoS) attacks.
What do botnets steal?
A botnet is a set of devices with an Internet connection, each of which runs one or more robots. Botnets can be used to carry out DDoS (Distributed Denial-of-Service) attacks, steal data, send spam, and allow an attacker to access a device and its connection.
What are botnets used for? They are mainly used to send spam, often malware, from any robot. For example, Cutwail’s botnet can send up to 74 billion messages a day. They are also used to distribute robots to recruit more computers into the botnet.
What started as the activity of geeky hackers has become a multibillion pound international criminal industry?
Cybercrime is one step ahead. What started as outrageous hackers has become a multi-billion pound international criminal industry. Not only is computer crime growing exponentially, it is mutating faster than it can be curbed.
What started cybercrime?
As a criminal activity, it began with hackers gaining illegal access to high-level computer networks. Some examples of cybercrime include credit card and identity theft, network intrusion, and software piracy. Federal laws related to the Computer Fraud and Abuse Act (CFAA), such as 18 U.S.C.
When did Cyber Crimes first start?
Hacking in the 1980s In fact, there was no real cybercrime until the 1980s. One person hacked into another person’s computer to find, copy, or manipulate personal information and information. The first person to be convicted of cybercrime was Ian Murphy, also known as Captain Zap, and this happened in 1981.
What was the first recorded cyber crime?
1834 – French telegraph system – A couple of thieves hack into the French telegraph system and steal information from the financial markets, effectively carrying out the world’s first cyber attack.
What are the activities of cyber criminals?
Cybercrime can involve many different types of for-profit criminal activity, including ransom attacks, email and Internet fraud, and identity fraud, as well as attempts to steal financial account, credit, or other payment card information.
What is social en?
Social engineering is a term used for many malicious activities that are done through human interaction. It uses psychological manipulation to entice users to make security mistakes or provide sensitive information.
What is social engineering and how does it work? Social manipulation is a technique used by criminals and cybercriminals to entice users to disclose confidential information. The data obtained is then used to gain access to the systems and to take action to the detriment of the person or organization whose data have been disclosed.
What is social engineering in simple words?
Social manipulation is the art of manipulating people so that they give up confidential information.
What is social engineering and examples?
Attacks on social manipulation are a type of cybercrime in which an attacker fools the target through impersonation. They may pretend to be your boss, a supplier, someone on our IT team, or your delivery company. No matter who they are, their motivation is always the same – to get money or data.
What does social engineering mean?
Social manipulation refers to any technique designed to induce a target to disclose specific information or perform a specific activity for illegal reasons.
What does social engineering mean kids?
Facts about children’s encyclopedia. Social manipulation (also known as “social manipulation”) is a type of self-confidence trick to influence people to obtain illegally sensitive information (eg passwords, credit card information).
What is social engineering simple?
Social manipulation is a manipulation technique that exploits human error to obtain private information, access or valuables. In the case of cybercrime, these “human hacking” frauds tend to lure unsuspecting users to disclose data, spread malware or provide access to restricted systems.
What are examples of social engineering?
The following are the five most common forms of digital social manipulation attack.
- Lure. As the name suggests, deception attacks use false promise to arouse the victim’s greed or curiosity. …
- Intimidation. Intimidation involves bombarding victims with false positives and fictitious threats. …
- Making an excuse. …
- Phishing. …
- Spear phishing.
What is social engineering explain with example?
Social manipulation is a manipulation technique that exploits human error to obtain private information, access or valuables. In the case of cybercrime, these “human hacking” frauds tend to lure unsuspecting users to disclose data, spread malware or provide access to restricted systems.
What are the 5 social engineering attacks?
Social manipulation is a term that covers a wide range of malicious activities. For this article, we will focus on the five most common types of attacks that social engineers use to target their victims. These are phishing, pretext, lure, quid pro quo and tracing.
What is the most common social engineering?
Phishing: the most common form of social technology Phishing is a form of email fraud in which someone sends an email claiming to be from a trusted company or person.
What are the 5 social engineering attacks?
Social manipulation is a term that covers a wide range of malicious activities. For this article, we will focus on the five most common types of attacks that social engineers use to target their victims. These are phishing, pretext, lure, quid pro quo and tracing.
What is the most common social engineering attack?
Phishing attacks are the most common attacks using social manipulation techniques. Attackers use email, social media, instant messaging, and SMS to trick victims into providing sensitive information or visiting malicious URLs in an attempt to harm their systems.
What is social engineering attack example?
Phishing: The most common way to use social manipulation tactics is for hackers to use misleading emails, websites, and text messages to steal sensitive personal or organizational information from unsuspecting victims. Deception: This type of attack can take place online or in a physical environment.



Comments are closed.